HAProxy Monitoring
What Is HAProxy?
HAProxy, short for High Availability Proxy, is a popular open-source software widely used for load balancing and proxying for TCP and HTTP-based applications. It is known for its reliability, performance, and feature-rich nature, making it a staple in server infrastructure for distributing workloads efficiently.
Monitoring HAProxy With Netdata
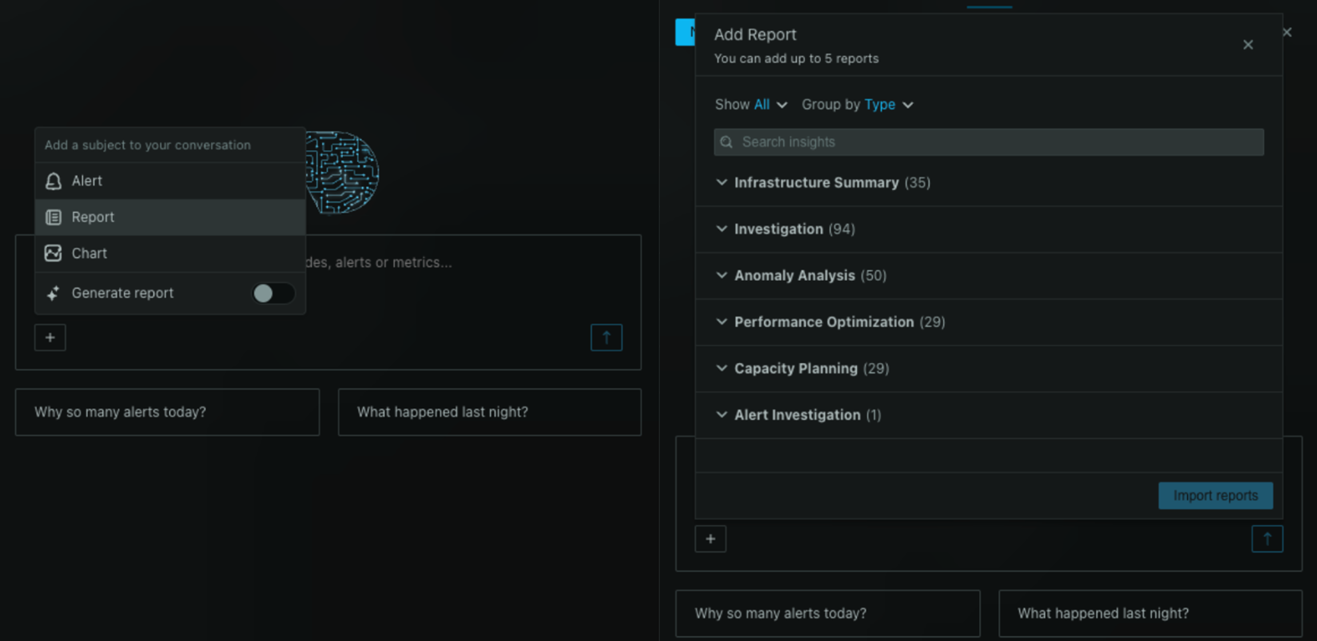
Monitoring HAProxy is crucial for ensuring your application infrastructure performs optimally and remains highly reliable. Netdata offers comprehensive and real-time monitoring of HAProxy, delivering rich visualization of health and performance metrics. By leveraging such a tool, you can observe metrics like response times, session rates, and network throughput in a live, interactive interface. You can get started by checking out the Live Demo or signing up for a free trial.
Why Is HAProxy Monitoring Important?
Monitoring HAProxy allows you to:
- Identify performance bottlenecks and reduce latency.
- Optimize resource usage and ensure high availability.
- Detect anomalies with real-time alerts.
- Ensure service reliability and enhance user experience.
What Are The Benefits Of Using HAProxy Monitoring Tools?
Using effective HAProxy monitoring tools, like Netdata, enables teams to track performance metrics in real-time, quickly diagnose issues, and maintain a healthy, scalable infrastructure. This ensures applications remain accessible and performant under varying load conditions.
Understanding HAProxy Performance Metrics
A range of metrics is available for monitoring HAProxy, providing insights into its performance:
Global Metrics
- Current Sessions (
haproxy.backend_current_sessions): The number of active sessions at any given time. - Sessions Rate (
haproxy.backend_sessions): The rate at which sessions are occurring. - Average Response Time (
haproxy.backend_response_time_average): The average response time for the last 1024 successful connections. - Average Queue Time (
haproxy.backend_queue_time_average): The average time requests spend in the queue. - Current Queue (
haproxy.backend_current_queue): The number of requests currently queued.
Proxy Metrics
- HTTP Responses (
haproxy.backend_http_responses): Breakdown of HTTP responses by status code class. - Network I/O (
haproxy.backend_network_io): Measurement of network traffic both inbound and outbound.
Advanced HAProxy Performance Monitoring Techniques
Advanced techniques for HAProxy monitoring include the setup of custom alerts, the use of anomaly detection for proactive problem-solving, and correlating HAProxy data with other system metrics for comprehensive insight.
Diagnose Root Causes Or Performance Issues Using Key HAProxy Statistics & Metrics
By monitoring these key statistics, you can swiftly diagnose any issues affecting HAProxy’s performance, allowing for fast mitigation and minimal service disruption. Learn more from our HAProxy collector documentation.
Whether you aim to maximize uptime or optimize the performance of HAProxy, Netdata provides the tools and insights necessary for effective monitoring. View Netdata Live or explore more by signing up.
FAQs
What Is HAProxy Monitoring?
HAProxy monitoring involves tracking various performance metrics of the HAProxy server, helping ensure load balancing across resources and maintaining performance.
Why Is HAProxy Monitoring Important?
It ensures your application’s performance, availability, and reliability are maintained by providing actionable insights and timely alerts.
What Does An HAProxy Monitor Do?
An HAProxy monitor captures and visualizes data about session rates, response times, network throughput, and more to help identify and resolve performance issues.
How Can I Monitor HAProxy In Real Time?
You can monitor HAProxy in real time using tools like Netdata, which offers a real-time monitoring platform to visually track various system metrics.